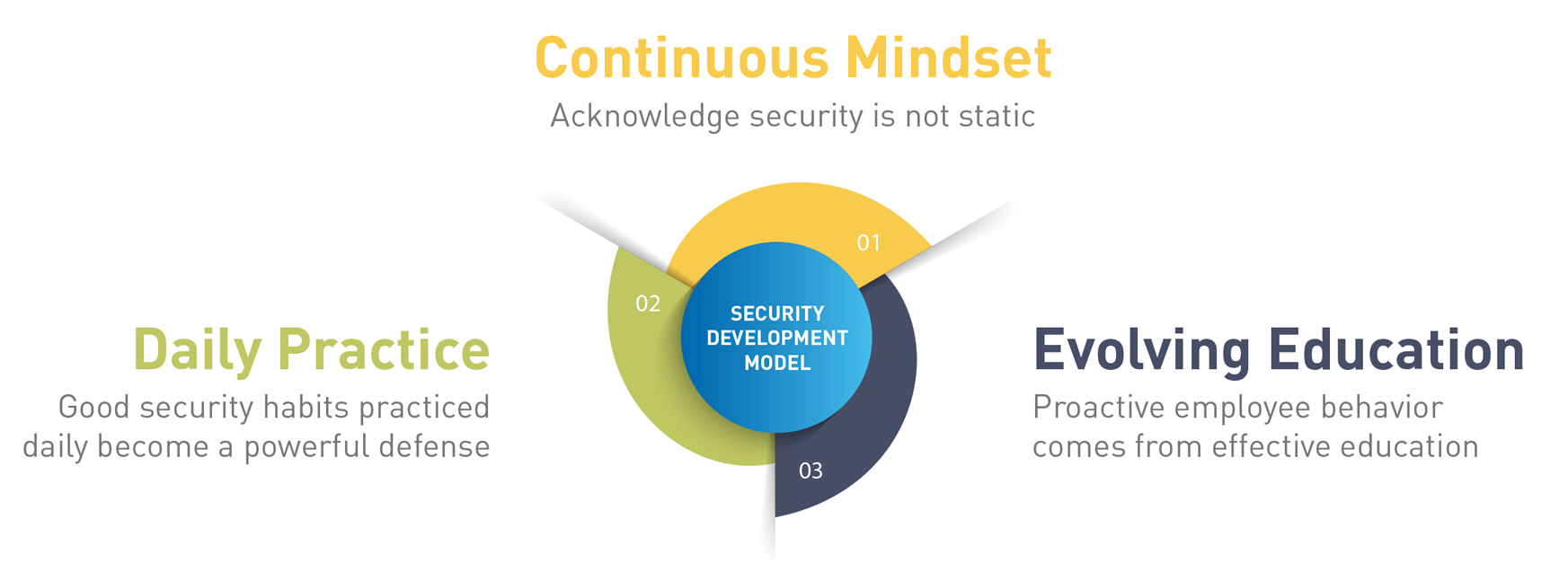
“Successful security is a continuous mindset, daily practice and education that evolves as the security landscape changes. There is no singular magic bullet, it’s a constant enforcement of governance, compliance, and policy. ”
Successful Security
Successful security programs rely on a proactive and structured practice that detects and mitigates internal as well as external threats using software, hardware, education, consistent training and intelligent operational safeguards. While there is no single solution due to the innovative and perpetual evolution of new threats, this multipronged approach provides a baseline that businesses can scale and rely on over time.
Our Process
We begin with a global audit of a client’s existing technology infrastructure and operational requirements. This audit covers everything from simple components like email and Slack messaging to more complex operations like data back up, attack surface management and secure network access points. This gets further broken down to articulate incoming and outgoing data sources and associated risks. We also assess user practices and education on security practices.
Once we have a comprehensive image of a client’s technology foot print we architect a security blueprint and then layer on relevant security components and practices. Sequentially we work with the client to verify viability of the blueprint. When a viable security architecture is completed we begin to build an implementation plan and outline ancillary maintenance and monitoring.
Regulatory Compliance
Our extensive work with the US military, SAP National Security Services and companies bound by Sarbanes Oxley and SIPC requirements have made our team facile with all manner of regulatory and other governmental requirements.
Testing & Audit
The dynamic nature of threats makes testing and periodic audits a non-negotiable practice. We help clients meet requirements, optimize security practices and minimize cost and disruptions.